Course Highlights
 Training Mode
Training Mode
Classroom and Online Learning Method
Learning Method
Lecture & Self-Study Duration
Duration
8 Months Training Hours
Training Hours
3 Hours per day Hands on Labs
Hands on Labs
Yes Study Material
Study Material
Yes Certificate
Certificate
Yes Batches
Batches
Weekdays (Mon-Fri) & Weekend (Sat-Sun) Price
Price
Enquire now


Enquire Now
CCIE Security v6.1 Zero to Hero Course Details
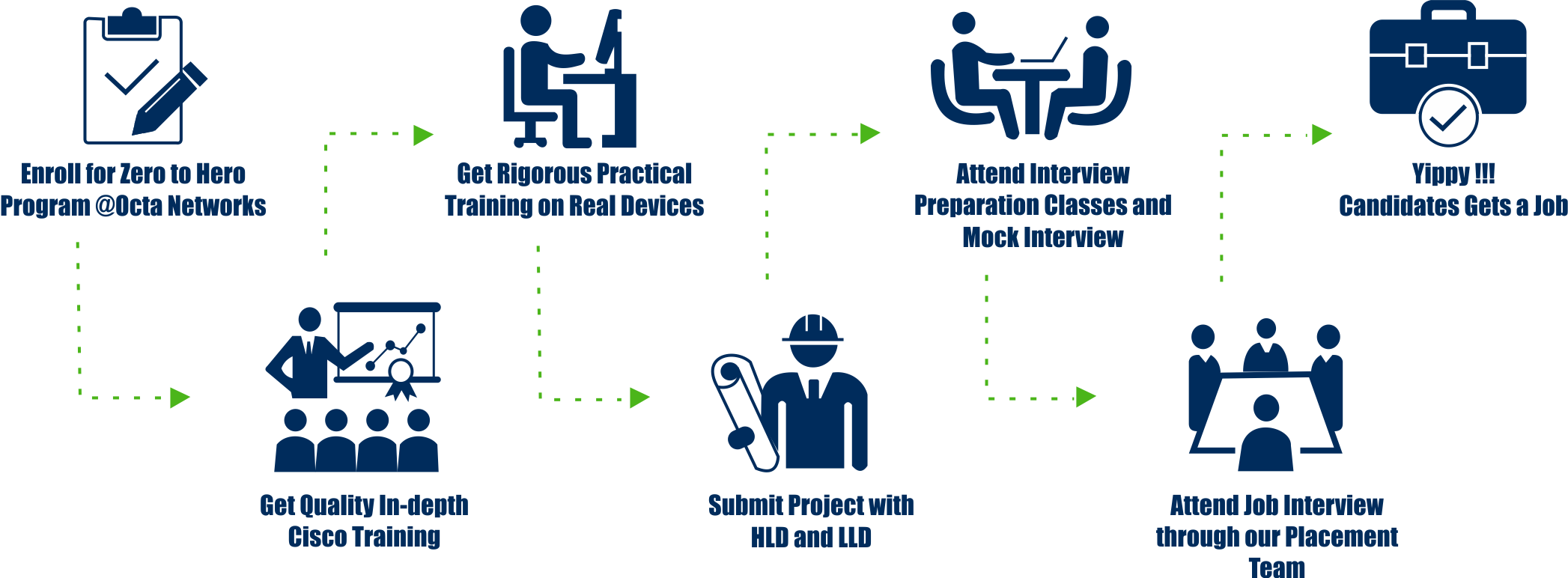
The CCIE Security Zero to Hero course is an integrated training program designed for graduates and fresher’s as per the Industry requirements. CCIE Security Zero to Hero course is 100% Job Guarantee program and one of the most popular program Octa Networks ever had.
Octa Networks has specialized itself in Job guaranteed courses after thorough discussions and consultation with industry experts like Hiring Manager, Technical Managers, Team leaders, HR, Recruitment Officers and much more. Our Zero to Hero Program focuses on molding candidates as per the Industry needs. These courses are designed as per industry needs and are planned in such a way that candidate is guaranteed to get a job after successful completion of the training.
The course covers technical knowledge right from the foundation level up to the expert level and that’s why this program is called Zero to Hero program. This program includes: New CCNA (200-301) + CCNP Enterprise (ENARSI 300-410) + Python for Network Engineers + CCNP Security (SCOR 350-701 + SNCF 300-710) + CCIE Security Training. Apart from theory, this program includes rigorous hands-on lab sessions, also comprises of industry experts’ sessions, practice tests, group discussions, technical presentations, resume preparation, topology preparation, interview preparation, and much more. Upon completion of this program, you will be a IT Superhero who can design, implement, operate, diagnose and troubleshoot complex Security infrastructure.
Octa Networks is the only cisco training Institute in India to give you “On Paper Job Guarantee” the day you enroll for our CCIE Security Zero to Hero program.
Octa Networks is also world’s largest and only cisco training Institute having real devices for ALL CCIE tracks. Candidates can touch and feel routers, switches, next generation firewalls, next generation IPS, nexus 7000, nexus 9000, wireless controllers, access points, IP phones and basically all the devices used in all of the cisco CCIE tracks. No training center in the world houses all of the CCIE devices under one roof.
Octa Networks is the World’s only Cisco Training Center with 2 x Octa CCIE's as Mentors with 25+ years of experience among themselves and has one of the best Cisco CCIE Certified Trainers to motivate, nurture and guide you throughout your Cisco Certification career path.
Our Candidates are working with the best of the IT companies in the world like Cisco, Amazon, Vmware, World Wide, Dimension Data, NTT, Orange, Accenture, Tech-Mahindra, HCL, TCS, Wipro, British-Telecom, Mphassis, Intuit are just few names from the never-ending list.
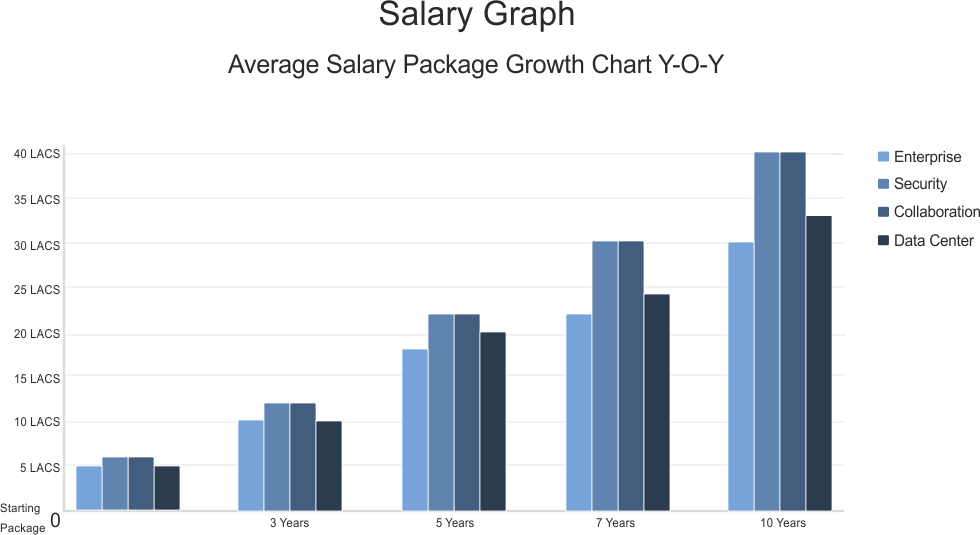
Our candidates are not only working in India but also in countries like USA, Canada, Europe, Qatar, Dubai, Abu Dhabi, Singapore, Australia and many more countries. Their salary packages vary from 10 to 50 Lacs INR per annum in India and 100,000 to 300,000 USD (60 Lacs to 2 cr. in INR) per annum in international countries.
CCIE Security v6.0 Zero to Hero Course overview
Duration
- 8 months of Instructor-led classroom training
- 8 months of instructor-led online training
Who should enroll?
- Undergraduates/Graduates from BCA, BE, BSC, BCOM, BA Background or Diploma Holders who are interested in Enterprise Security Domain
- Admission to this training program is given only after face to face discussion with our Training counselors
What you’ll learn in this course?
- Learn from basic to advance level of Enterprise Security technologies on the Cisco specific environment
- Get real world practical exposure on technologies used in Secured Enterprise networks
- Other than technical skills, you will also learn soft skills
How you'll benefit
- CCIE professionals are highest paid professionals in the IT industry.
- CCIE is accepted globally as the most prestigious networking certification in the industry. CCIE tag can surely give you a plethora of job opportunities across diverse countries. CCIE is your ticket to abroad.
- Job opportunities will increase manifolds as numerous top IT companies requires highly skilled CCIE Certified professionals for Implementing, Managing, Operating and Troubleshooting their or client complex networks.
- The demand for CCIE certified professionals will not be fulfilled in the years to come, thats why the fear of recession is barely any concern for CCIE professionals. With CCIE your career is secured.
- Being a CCIE not only commands respect and admiration from employers but it also instill confidence and credibility among your customers. Clients start finding you reliable especially if you are working as a consultant.
What is CCIE Security Zero to Hero Course Curriculum?
The course covers technical knowledge right from the foundation level up to the expert level and that’s why this program is called Zero to Hero program
Duration
- 1 Month of Instructor-led classroom training
- 1 Month of Virtual instructor-led online training
What you’ll learn in this course?
Upon completion of this course, candidates will have the skills and knowledge to:
- Network Fundamentals
- How to install, operate, configure, and verify basic IPv4 and IPv6 networks
- Configuring network components such as switches, routers, and wireless LAN controllers
- Managing network devices; and identifying basic security threats
- Foundation in network programmability, automation, and software-defined networking
How you'll benefit
- Learn the knowledge and skills to install, configure, and operate a small- to medium-sized network
- Gain a foundation in the essentials of networking, security, and automation
- Prepare for the 200-301 CCNA exam certification
Prerequisite
Before taking the CCNA course, candidates should be familiar with
- Basic computer literacy
- Basic PC operating system navigation skills
- Basic Internet usage skills
- Basic IP address knowledge
- Good understanding of network fundamentals
Hands-on Labs?
- Get Started with Cisco Command-Line Interface (CLI)
- Observe How a Switch Operates
- Perform Basic Switch Configuration
- Implement the Initial Switch Configuration
- Inspect TCP/IP Applications
- Configure an Interface on a Cisco Router
- Configure and Verify Layer 2 Discovery Protocols
- Implement an Initial Router Configuration
- Configure Default Gateway
- Explore Packet Forwarding
- Troubleshoot Switch Media and Port Issues
- Troubleshoot Port Duplex Issues
- Configure Basic IPv6 Connectivity
- Configure and Verify IPv4 Static Routes
- Configure IPv6 Static Routes
- Implement IPv4 Static Routing
- Implement IPv6 Static Routing
- Configure VLAN and Trunk
- Troubleshoot VLANs and Trunk
- Configure a Router on a Stick
- Implement Multiple VLANs and Basic Routing Between the VLANs
- Configure and Verify Single-Area OSPF
- Configure and Verify EtherChannel
- Improve Redundant Switched Topologies with EtherChannel
- Configure and Verify IPv4 ACLs
- Implement Numbered and Named IPv4 ACLs
- Configure a Provider-Assigned IPv4 Address
- Configure Static NAT
- Configure Dynamic NAT and Port Address Translation (PAT)
- Implement PAT
- Log into the WLC
- Monitor the WLC
- Configure a Dynamic (VLAN) Interface
- Configure a DHCP Scope
- Configure a WLAN
- Define a Remote Access Dial-In User Service (RADIUS) Server
- Explore Management Options
- Explore the Cisco DNA™ Center
- Configure and Verify NTP
- Configure System Message Logging
- Create the Cisco IOS Image Backup
- Upgrade Cisco IOS Image
- Configure WLAN Using Wi-Fi Protected Access 2 (WPA2) Pre-Shared Key (PSK) Using the GUI
- Secure Console and Remote Access
- Enable and Limit Remote Access Connectivity
- Secure Device Administrative Access
- Configure and Verify Port Security
- Implement Device Hardening
What to expect in the exam?
- The 200-301 CCNA exam certifies your knowledge and skills related to network fundamentals, network access, IP connectivity, IP services, security fundamentals, and automation and programmability.
- After you pass 200-301 CCNA, you earn CCNA certification.
Duration
- 1 month of Instructor-led classroom training
- 1 month of instructor-led online training
What you’ll learn in this course?
- Install, configure, operate, and troubleshoot an enterprise wired network.
- Advance routing and infrastructure technologies covered in ENCOR
How you'll benefit
Upon completion of this course, candidates will have the skills and knowledge to:
- Gain the knowledge you need to install, configure, operate, and troubleshoot an enterprise network
- Qualify for professional-level job roles in advance routing and services
- Prepare for the Implementing Cisco Enterprise Advanced Routing and Services (300-410 ENARSI) exam.
Prerequisites
To fully benefit from this course, you should have the following knowledge and skills:
- General understanding of network fundamentals
- Basic knowledge of how to implement LANs
- General understanding of how to manage network devices
- General understanding of how to secure network devices
- Basic knowledge of network automation
Training Outline
- Implementing EIGRP
- Optimizing EIGRP
- Troubleshooting EIGRP
- Implementing OSPF
- Optimizing OSPF
- Troubleshooting OSPF
- Implementing Internal Border Gateway Protocol (IBGP)
- Optimizing BGP
- Implementing MP-BGP
- Troubleshooting BGP
- Configuring Redistribution
- Troubleshooting Redistribution
- Implementing Path Control
- Exploring MPLS
- Introducing MPLS L3 VPN Architecture
- Introducing MPLS L3 VPN Routing
- Configuring Virtual Routing and Forwarding (VRF)-Lite
- Implementing DMVPN
- Implementing DHCP
- Troubleshooting DHCP
- Introducing IPv6 First Hop Security
- Securing Cisco Routers
- Troubleshooting Infrastructure Security and Services
Hands-on Labs
- Configure EIGRP Using Classic Mode and Named Mode for IPv4 and IPv6
- Verify the EIGRP Topology Table
- Configure EIGRP Stub Routing, Summarization, and Default Routing
- Configure EIGRP Load Balancing and Authentication
- LAB: Troubleshoot EIGRP Issues
- Configure OSPFv3 for IPv4 and IPv6
- Verify the Link-State Database
- Configure OSPF Stub Areas and Summarization
- Configure OSPF Authentication
- Troubleshoot OSPF
- Implement Routing Protocol Redistribution
- Manipulate Redistribution
- Manipulate Redistribution Using Route Maps
- Troubleshoot Redistribution Issues
- Implement PBR
- Configure IBGP and External Border Gateway Protocol (EBGP)
- Implement BGP Path Selection
- Configure BGP Advanced Features
- Configure BGP Route Reflectors
- Configure MP-BGP for IPv4 and IPv6
- Troubleshoot BGP Issues
- Implement PBR
- Configure Routing with VRF-Lite
- Implement Cisco IOS DMVPN
- Obtain IPv6 Addresses Dynamically
- Troubleshoot DHCPv4 and DHCPv6 Issues
- Troubleshoot IPv4 and IPv6 Access Control List (ACL) Issues
- Configure and Verify Control Plane Policing
- Configure and Verify Unicast Reverse Path Forwarding (uRPF)
What to expect in the exam
- 300-410 ENARSI exam tests your knowledge of implementation and troubleshooting for advanced routing technologies and services.
- After you pass 300-410 ENARSI, You earn the Cisco Certified Specialist – Enterprise Advanced Infrastructure Implementation certification.
- You satisfy the concentration requirement for the new CCNP Enterprise certification. To complete your CCNP Enterprise certification, you must pass 350-401 ENCOR exam.
Course Duration
- 1 month of Instructor-led classroom training
- 1 month of instructor-led online training
Who should enroll?
- Network administrators
- Professionals who are interested in network programmability and automation
What you’ll learn in this course?
- Understand network programmability and Python version 3
- Understand how to automate the configuration of network devices with python
- Understand how to leverage NAPALM for network automation
- Understand how to quickly start guide using Telnet and SSH
- Understand how to use Netmiko for SSH connections to routers and switches
- Understand how to scale your network scripts
Prerequisites
The knowledge and skills that a learner must have before attending this course are as follows:
- Experience with network management (CCNA-level recommended)
Training Outline
The Python Programming Environment
- The Python Interactive Interpreter
- Running the Interpreter
- Running code inside the Interpreter
- Learning with the Interpreter
- Running Your Python Scripts
- Saving Your Source Files
- Executing Your Source Files
- What does the Shebang (#!) Line Do?
Python Fundamentals
- The Python Object/Execution Model
- Everything is an Object
- Two Types of Objects
- Statements and Expressions
- Variables
- Traditional Variable Concepts
- Variables in Python
- Data Types
- Data Types :: Strings
- Data Types :: Integers
- Data Types :: Floats
- Data Types :: Lists
- Data Types :: Dictionaries
- Data Types :: Tuples
- Control Structures
- Control Structures :: if/else/elif Statements
- Control Structures :: for loops
- Control Structures :: while loops
- Control Structures :: Breaking Out of Loops
- Control Structures :: The 'pass' Statement
- Control Structures :: The ‘continue’ Statement
- Functions
- Functions :: What is Scope?
- Functions & Arguments
- Functions :: Positional Arguments
- Functions :: Keyword Arguments
(Slightly) More Advanced Python
- Exceptions
- Exceptions :: What are Exceptions?
- Exceptions :: Catching Exceptions
- Exceptions :: The "try/finally" Clause
- Working with Files and Directories
- Using 'open'
- File Object Modes
- File Object Methods
- The 'with' Statement
- Complex Data Structures
- How to Think About Data
- List
- Tuples
- Set
- Disctionary
- Example One :: A List of Lists
- Example Two :: A Lists of Dictionaries
- Example Three :: A Dictionary of Dictionaries
- Example Four :: A Dictionary of Set and Lists
- Maintaining State
- Maintaining State :: XML
- Maintaining State :: YAML
- Maintaining State :: JSON
- Modules
- Finding and Using Modules
- Creating Your Own Modules
- Object Orientation
- What is a Class
- Static Methods
- Member Variables
- Member Functions
- Constructors
- Singleton Class
- MVC Design Pattern
- Observer Design Pattern
- Extra Topics suitable for Devnets
- String formatting
- Programming your device in GNS3 using Python
Hands-on Labs
Python Foundations
- Lists
- Dictionaries
- Loops
- Function
- Working with Files
- Troubleshooting Python Scripts
Python Libraries
- Introduction
- Python Module
- Python Package
Custom Python Libraries
Working with XML in Python
Working with YAML in Python
Working with JSON objects in Python
- Yang Data Models
- Model-Driven Programmability Stack
- REST
- NETCONF
NX-API Discovery
- NX-API CLI Part 2
- NETCONF
- Python on Box
- NX-API REST
What to expect in the exam?
As of date there is no associated certification or exam for this course.
Duration
- 1 month of Instructor-led classroom training
- 1 month of instructor-led online training
What you’ll learn in this course?
- Implement core Cisco Security solutions to provide advanced threat protection against cyberSecurity attacks
- Security for networks, cloud and content, endpoint protection, secure network access, visibility, and enforcements
- Hands-on experience deploying Cisco Firepower, Next-Generation Firewall and Cisco Adaptive Security Appliance (ASA) Firewall
- Configuring access control policies, mail policies, and 802.1X Authentication; and more
How you'll benefit
Upon completion of this course, candidates will have the skills and knowledge to:
- Gain extensive hands-on experience implementing core Security technologies and learn best practices using Cisco Security solutions
- Prepare for the Implementing and Operating Cisco Security Core Technologies (350-701 SCOR) exam
Prerequisites
Knowledge and skills you should have before attending this course:
- Skills and knowledge equivalent to those learned in new CCNA
- Familiarity with Ethernet and TCP/IP networking
- Working knowledge of the Windows operating system
- Working knowledge of Cisco IOS networking and concepts
- Familiarity with basics of networking Security concepts
Training Outline
- Describing Information Security Concepts*
- Information Security Overview
- Assets, Vulnerabilities, and Countermeasures
- Managing Risk
- Vulnerability Assessment
- Understanding Common Vulnerability Scoring System (CVSS)
- Describing Common TCP/IP Attacks*
- Legacy TCP/IP Vulnerabilities
- IP Vulnerabilities
- Internet Control Message Protocol (ICMP) Vulnerabilities
- TCP Vulnerabilities
- User Datagram Protocol (UDP) Vulnerabilities
- Attack Surface and Attack Vectors
- Reconnaissance Attacks
- Access Attacks
- Man-in-the-Middle Attacks
- Denial of Service and Distributed Denial of Service Attacks
- Reflection and Amplification Attacks
- Spoofing Attacks
- Dynamic Host Configuration Protocol (DHCP) Attacks
- Describing Common Network Application Attacks*
- Password Attacks
- Domain Name System (DNS)-Based Attacks
- DNS Tunneling
- Web-Based Attacks
- HTTP 302 Cushioning
- Command Injections
- SQL Injections
- Cross-Site Scripting and Request Forgery
- Email-Based Attacks
- Describing Common Endpoint Attacks*
- Buffer Overflow
- Malware
- Reconnaissance Attack
- Gaining Access and Control
- Gaining Access via Social Engineering
- Gaining Access via Web-Based Attacks
- Exploit Kits and Rootkits
- Privilege Escalation
- Post-Exploitation Phase
- Angler Exploit Kit
- Describing Network Security Technologies
- Defense-in-Depth Strategy
- Defending Across the Attack Continuum
- Network Segmentation and Virtualization Overview
- Stateful Firewall Overview
- Security Intelligence Overview
- Threat Information Standardization
- Network-Based Malware Protection Overview
- Intrusion Prevention System (IPS) Overview
- Next Generation Firewall Overview
- Email Content Security Overview
- Web Content Security Overview
- Threat Analytic Systems Overview
- DNS Security Overview
- Authentication, Authorization, and Accounting Overview
- Identity and Access Management Overview
- Virtual Private Network Technology Overview
- Network Security Device Form Factors Overview
- Deploying Cisco ASA Firewall
- Cisco ASA Deployment Types
- Cisco ASA Interface Security Levels
- Cisco ASA Objects and Object Groups
- Network Address Translation
- Cisco ASA Interface Access Control Lists (ACLs)
- Cisco ASA Global ACLs
- Cisco ASA Advanced Access Policies
- Cisco ASA High Availability Overview
- Deploying Cisco Firepower Next-Generation Firewall
- Cisco Firepower NGFW Deployments
- Cisco Firepower NGFW Packet Processing and Policies
- Cisco Firepower NGFW Objects
- Cisco Firepower NGFW Network Address Translation (NAT)
- Cisco Firepower NGFW Prefilter Policies
- Cisco Firepower NGFW Access Control Policies
- Cisco Firepower NGFW Security Intelligence
- Cisco Firepower NGFW Discovery Policies
- Cisco Firepower NGFW IPS Policies
- Cisco Firepower NGFW Malware and File Policies
- Deploying Email Content Security
- Cisco Email Content Security Overview
- Simple Mail Transfer Protocol (SMTP) Overview
- Email Pipeline Overview
- Public and Private Listeners
- Host Access Table Overview
- Recipient Access Table Overview
- Mail Policies Overview
- Protection Against Spam and Graymail
- Anti-virus and Anti-malware Protection
- Outbreak Filters
- Content Filters
- Data Loss Prevention
- Email Encryption
- Deploying Web Content Security
- Cisco Web Security Appliance (WSA) Overview
- Deployment Options
- Network Users Authentication
- Secure HTTP (HTTPS) Traffic Decryption
- Access Policies and Identification Profiles
- Acceptable Use Controls Settings
- Anti-Malware Protection
- Deploying Cisco Umbrella*
- Cisco Umbrella Architecture
- Deploying Cisco Umbrella
- Cisco Umbrella Roaming Client
- Managing Cisco Umbrella
- Cisco Umbrella Investigate Overview and Concepts
- Explaining VPN Technologies and Cryptography
- VPN Definition
- VPN Types
- Secure Communication and Cryptographic Services
- Keys in Cryptography
- Public Key Infrastructure
- Introducing Cisco Secure Site-to-Site VPN Solutions
- Site-to-Site VPN Topologies
- IPsec VPN Overview
- IPsec Static Crypto Maps
- IPsec Static Virtual Tunnel Interface
- Dynamic Multipoint VPN
- Cisco IOS FlexVPN
- Deploying Cisco IOS VTI-Based Point-to-Point IPsec VPNs
- Cisco IOS VTIs
- Static VTI Point-to-Point IPsec Internet Key Exchange (IKE) v2 VPN Configuration
- Deploying Point-to-Point IPsec VPNs on the Cisco ASA and Cisco Firepower NGFW
- Point-to-Point VPNs on the Cisco ASA and Cisco Firepower NGFW
- Cisco ASA Point-to-Point VPN Configuration
- Cisco Firepower NGFW Point-to-Point VPN Configuration
- Introducing Cisco Secure Remote Access VPN Solutions
- Remote Access VPN Components
- Remote Access VPN Technologies
- Secure Sockets Layer (SSL) Overview
- Deploying Remote Access SSL VPNs on the Cisco ASA and Cisco Firepower NGFW
- Remote Access Configuration Concepts
- Connection Profiles
- Group Policies
- Cisco ASA Remote Access VPN Configuration
- Cisco Firepower NGFW Remote Access VPN Configuration
- Explaining Cisco Secure Network Access Solutions
- Cisco Secure Network Access
- Cisco Secure Network Access Components
- AAA Role in Cisco Secure Network Access Solution
- Cisco Identity Services Engine
- Cisco TrustSec
- Describing 802.1X Authentication
- 1X and Extensible Authentication Protocol (EAP)
- EAP Methods
- Role of Remote Authentication Dial-in User Service (RADIUS) in 802.1X Communications
- RADIUS Change of Authorization
- Configuring 802.1X Authentication
- Cisco Catalyst® Switch 802.1X Configuration
- Cisco Wireless LAN Controller (WLC) 802.1X Configuration
- Cisco Identity Services Engine (ISE) 802.1X Configuration
- Supplicant 802.1x Configuration
- Cisco Central Web Authentication
- Describing Endpoint Security Technologies*
- Host-Based Personal Firewall
- Host-Based Anti-Virus
- Host-Based Intrusion Prevention System
- Application Whitelists and Blacklists
- Host-Based Malware Protection
- Sandboxing Overview
- File Integrity Checking
- Deploying Cisco Advanced Malware Protection (AMP) for Endpoints*
- Cisco AMP for Endpoints Architecture
- Cisco AMP for Endpoints Engines
- Retrospective Security with Cisco AMP
- Cisco AMP Device and File Trajectory
- Managing Cisco AMP for Endpoints
- Introducing Network Infrastructure Protection*
- Identifying Network Device Planes
- Control Plane Security Controls
- Management Plane Security Controls
- Network Telemetry
- Layer 2 Data Plane Security Controls
- Layer 3 Data Plane Security Controls
- Deploying Control Plane Security Controls*
- Infrastructure ACLs
- Control Plane Policing
- Control Plane Protection
- Routing Protocol Security
- Deploying Layer 2 Data Plane Security Controls*
- Overview of Layer 2 Data Plane Security Controls
- Virtual LAN (VLAN)-Based Attacks Mitigation
- Spanning Tree Protocol (STP) Attacks Mitigation
- Port Security
- Private VLANs
- Dynamic Host Configuration Protocol (DHCP) Snooping
- Address Resolution Protocol (ARP) Inspection
- Storm Control
- MACsec Encryption
- Deploying Layer 3 Data Plane Security Controls*
- Infrastructure Antispoofing ACLs
- Unicast Reverse Path Forwarding
- IP Source Guard
- Deploying Management Plane Security Controls*
- Cisco Secure Management Access
- Simple Network Management Protocol Version 3
- Secure Access to Cisco Devices
- AAA for Management Access
- Deploying Traffic Telemetry Methods*
- Network Time Protocol
- Device and Network Events Logging and Export
- Network Traffic Monitoring Using NetFlow
- Deploying Cisco Stealthwatch Enterprise*
- Cisco Stealthwatch Offerings Overview
- Cisco Stealthwatch Enterprise Required Components
- Flow Stitching and Deduplication
- Stealthwatch Enterprise Optional Components
- Stealthwatch Enterprise and ISE Integration
- Cisco Stealthwatch with Cognitive Analytics
- Cisco Encrypted Traffic Analytics
- Host Groups
- Security Events and Alarms
- Host, Role, and Default Policies
- Describing Cloud and Common Cloud Attacks*
- Evolution of Cloud Computing
- Cloud Service Models
- Security Responsibilities in Cloud
- Cloud Deployment Models
- Common Security Threats in Cloud
- Patch Management in the Cloud
- Security Assessment in the Cloud
- Securing the Cloud*
- Cisco Threat-Centric Approach to Network Security
- Cloud Physical Environment Security
- Application and Workload Security
- Cloud Management and API Security
- Network Function Virtualization (NFV) and Virtual Network Functions (VNF)
- Cisco NFV Examples
- Reporting and Threat Visibility in Cloud
- Cloud Access Security Broker
- Cisco CloudLock®
- OAuth and OAuth Attacks
- Deploying Cisco Stealthwatch Cloud*
- Cisco Stealthwatch Cloud for Public Cloud Monitoring
- Cisco Stealthwatch Cloud for Private Network Monitoring
- Cisco Stealthwatch Cloud Operations
- Describing Software-Defined Networking (SDN*)
- Software-Defined Networking Concepts
- Network Programmability and Automation
- Cisco Platforms and APIs
- Basic Python Scripts for Automation
Hands-on Labs
- Configure Network Settings and NAT on Cisco ASA
- Configure Cisco ASA Access Control Policies
- Configure Cisco Firepower NGFW NAT
- Configure Cisco Firepower NGFW Access Control Policy
- Configure Cisco Firepower NGFW Discovery and IPS Policy
- Configure Cisco NGFW Malware and File Policy
- Configure Listener, Host Access Table (HAT), and Recipient Access Table (RAT) on Cisco Email Security Appliance (ESA)
- Configure Mail Policies
- Configure Proxy Services, Authentication, and HTTPS Decryption
- Enforce Acceptable Use Control and Malware Protection
- Examine the Umbrella Dashboard
- Examine Cisco Umbrella Investigate
- Explore DNS Ransomware Protection by Cisco Umbrella
- Configure Static VTI Point-to-Point IPsec IKEv2 Tunnel
- Configure Point-to-Point VPN between the Cisco ASA and Cisco Firepower NGFW
- Configure Remote Access VPN on the Cisco Firepower NGFW
- Explore Cisco AMP for Endpoints
- Perform Endpoint Analysis Using AMP for Endpoints Console
- Explore File Ransomware Protection by Cisco AMP for Endpoints Console
- Explore Cisco Stealthwatch Security v6.9.3
- Explore Cognitive Threat Analytics (CTA) in Stealthwatch Security v7.0
- Explore the Cisco Cloudlock Dashboard and User Security
- Explore Cisco Cloudlock Application and Data Security
- Explore Cisco Stealthwatch Cloud
- Explore Stealthwatch Cloud Alert Settings, Watchlists, and Sensors
What to expect in the exam
- 350-701 SCOR exam tests your knowledge of implementing and operating core Security technologies .
- After you pass 350-701 SCOR, You earn the Cisco Certified Specialist – Security Core certification.
- You satisfy the core requirement for CCNP Security and CCIE Security certification. To complete your CCNP Security certification, pass any one of the concentration exam.
Duration
- 1 month of Instructor-led classroom training
- 1 month of instructor-led online training
What you’ll learn in this course?
- Configure Cisco Firepower Threat Defense technology
- Cisco Adaptive Security Appliance (ASA) to Cisco Firepower Threat Defense migration,
- Implement advanced Next-Generation Firewall (NGFW) and Next-Generation Intrusion Prevention System (NGIPS) features
- Configure site-to-site VPN, remote-access VPN, and SSL
How you'll benefit
Upon completion of this course, candidates will have the skills and knowledge to:
- Implement Cisco Firepower NGFW to provide advanced threat protection before, during, and after attacks
- Gain leading-edge skills for high-demand responsibilities focused on security
- Prepare for Securing Networks with Cisco Firepower Next Generation Firewall and IPS (300-710 SNCF) exam.
Prerequisites
Knowledge and skills you should have before attending this course:
- Knowledge of TCP/IP and basic routing protocols
- Familiarity with firewall, VPN, and Intrusion Prevention System (IPS) concepts
Training Outline
- Cisco Firepower Threat Defense Overview
- Examining Firewall and IPS Technology
- Firepower Threat Defense Features and Components
- Examining Firepower Platforms
- Examining Firepower Threat Defense Licensing
- Cisco Firepower Implementation Use Cases
- Cisco Firepower NGFW Device Configuration
- Firepower Threat Defense Device Registration
- FXOS and Firepower Device Manager
- Initial Device Setup
- Managing NGFW Devices
- Examining Firepower Management Center Policies
- Examining Objects
- Examining System Configuration and Health Monitoring
- Device Management
- Examining Firepower High Availability
- Configuring High Availability
- Cisco ASA to Firepower Migration
- Migrating from Cisco ASA to Firepower Threat Defense
- Cisco Firepower NGFW Traffic Control
- Firepower Threat Defense Packet Processing
- Implementing QoS
- Bypassing Traffic
- Cisco Firepower NGFW Address Translation
- NAT Basics
- Implementing NAT
- NAT Rule Examples
- Implementing NAT
- Cisco Firepower Discovery
- Examining Network Discovery
- Configuring Network Discovery
- Implementing Access Control Policies
- Examining Access Control Policies
- Examining Access Control Policy Rules and Default Action
- Implementing Further Inspection
- Examining Connection Events
- Access Control Policy Advanced Settings
- Access Control Policy Considerations
- Implementing an Access Control Policy
- Security Intelligence
- Examining Security Intelligence
- Examining Security Intelligence Objects
- Security Intelligence Deployment and Logging
- Implementing Security Intelligence
- File Control and Advanced Malware Protection
- Examining Malware and File Policy
- Examining Advanced Malware Protection
- Next-Generation Intrusion Prevention Systems
- Examining Intrusion Prevention and Snort Rules
- Examining Variables and Variable Sets
- Examining Intrusion Policies
- Site-to-Site VPN
- Examining IPsec
- Site-to-Site VPN Configuration
- Site-to-Site VPN Troubleshooting
- Implementing Site-to-Site VPN
- Remote-Access VPN
- Examining Remote-Access VPN
- Examining Public-Key Cryptography and Certificates
- Examining Certificate Enrollment
- Remote-Access VPN Configuration
- Implementing Remote-Access VPN
- SSL Decryption
- Examining SSL Decryption
- Configuring SSL Policies
- SSL Decryption Best Practices and Monitoring
- Detailed Analysis Techniques
- Examining Event Analysis
- Examining Event Types
- Examining Contextual Data
- Examining Analysis Tools
- Threat Analysis
- System Administration
- Managing Updates
- Examining User Account Management Features
- Configuring User Accounts
- System Administration
- Cisco Firepower Troubleshooting
- Examining Common Misconfigurations
- Examining Troubleshooting Commands
- Firepower Troubleshooting
Hands-on Labs
- Initial Device Setup
- Device Management
- Configuring High Availability
- Migrating from Cisco ASA to Cisco Firepower Threat Defense
- Implementing QoS
- Implementing NAT
- Configuring Network Discovery
- Implementing an Access Control Policy
- Implementing Security Intelligence
- Implementing Site-to-Site VPN
- Implementing Remote Access VPN
- Threat Analysis
- System Administration
- Firepower Troubleshooting
What to expect in the exam
- 300-710 SNCF exam tests your knowledge of Cisco Firepower Threat Defense and Firepower, including policy configurations, integrations, deployments, management, and troubleshooting.
- After you pass 300-710 SNCF, You earn the Cisco Certified Specialist – Network Security Firepower certification.
- You satisfy the concentration requirement for the CCNP Security certification. To complete your CCNP Security certification, you must pass 350-701 SCOR exam.
Duration
- 1 month of Instructor-led classroom training
- 1 month of instructor-led online training
What you’ll learn in this course?
- Deploy and use Cisco Firepower Next-Generation Intrusion Prevention System (NGIPS)
- Detection of network-based malware and file type, NGIPS tuning
- Configuration including application control, Security intelligence, firewall, and network-based malware and file controls
- File and malware inspection, Security intelligence, and network analysis policy configuration designed to detect traffic patterns;
- Configuration and deployment of correlation policies to take action based on events detected
How you'll benefit
Upon completion of this course, candidates will have the skills and knowledge to:
- Implement Cisco Firepower Next-Generation IPS to stop threats, address attacks, increase vulnerability prevention against suspicious files, and analyze for not-yet-identified threats
- Gain leading-edge skills for high-demand responsibilities focused on Security
- Prepare for Securing Networks with Cisco Firepower Next Generation Firewall and IPS (300-710 SNCF) exam.
Prerequisites
Knowledge and skills you should have before attending this course:
- Technical understanding of TCP/IP networking and network architecture.
- Basic familiarity with the concepts of Intrusion Detection Systems (IDS) and IPS.
Training Outline
- Cisco Firepower Threat Defense Overview
- Cisco Firepower NGFW Device Configuration
- Cisco Firepower NGFW Traffic Control
- Cisco Firepower Discovery
- Implementing Access Control Policies
- Security Intelligence
- File Control and Advanced Malware Protection
- Next-Generation Intrusion Prevention Systems
- Network Analysis Policies
- Detailed Analysis Techniques
- Cisco Firepower Platform Integration
- Alerting and Correlation Policies
- System Administration
- Cisco Firepower Troubleshooting
Hands-on Labs
- Initial Device Setup
- Device Management
- Configuring Network Discovery
- Implementing and Access Control Policy
- Implementing Security Intelligence
- File Control and Advanced Malware Protection
- Implementing NGIPS
- Customizing a Network Analysis Policy
- Detailed Analysis
- Configuring Cisco Firepower Platform Integration with Splunk
- Configuring Alerting and Event Correlation
- System Administration
- Cisco Firepower Troubleshooting
What to expect in the exam
- 300-710 SNCF exam tests your knowledge of Cisco Firepower Threat Defense and Firepower, including policy configurations, integrations, deployments, management, and troubleshooting.
- After you pass 300-710 SNCF, You earn the Cisco Certified Specialist – Network Security Firepower certification.
- You satisfy the concentration requirement for the CCNP Security certification. To complete your CCNP Security certification, you must pass 350-701 SCOR exam.
Course Duration
- 2 months of Instructor-led classroom training
- 2 months of instructor-led online training
Who should enroll?
- Network engineers with Core exam - Implementing and Operating Cisco Security Core Technologies (SCOR 350-701)
- Network engineer with at least five to seven years of professional experience with designing, deploying, operating and optimizing enterprise security technologies
- Network engineers need to use an expert-level problem-solving process that includes options analysis to support complex network technologies and topologies
- Network designers that design and support complex network technologies and topologies
- Students and professionals in the IT and Technologies sector who wish to enhance their knowledge and acquire an internationally recognized professional certification which can improve their job prospects
What you’ll learn in this course?
- Implement core Cisco security solutions to provide advanced threat protection against cyber security attacks
- Security for networks, cloud and content, endpoint protection, secure network access, visibility, and enforcements
- Configure Cisco Firepower Threat Defense technology
- Implement advanced Next-Generation Firewall (NGFW) and Next-Generation Intrusion Prevention System (NGIPS) features
- Deploy and use Cisco Firepower Next-Generation Intrusion Prevention System (NGIPS)
- Detection of network-based malware and file type, NGIPS tuning
- Configuration including application control, security intelligence, firewall, and network-based malware and file controls
- Deploy and use Cisco Identity Services Engine (ISE) v2.4
- Highly secure access control across wired, wireless, and VPN connections
- Implement, use, and maintain Cisco Web Security Appliance (WSA)
- Provide advanced protection for business email and control against web security threats
- Deploy proxy services, use authentication, implement policies to control HTTPS traffic and access
- Deploy and troubleshoot traditional Internet Protocol Security (IPsec), Dynamic Multipoint Virtual Private Network (DMVPN), FlexVPN, and remote access VPN
- Design advanced automated security solutions for your network
How you'll benefit
Upon completion of this course, candidates will have the skills and knowledge to:
- Create, analyze, validate and optimize network designs, which is the base for all deployment activities
- Understand the capabilities of different technologies, solutions, and services
- Translate customer requirements into solutions
- Assess readiness to support proposed solutions
- Deploying, operating and optimizing network technologies and solutions
- As a CCIE (Cisco Certified Internetwork Expert), you can position yourself as a technical leader in the dynamic world of enterprise networks
- With the CCIE Security v6.1 certification, you get to combine technical expertise with design skills which can add tremendous value to your skillsets
- CCIE certification enhances your skills across the lifecycle of the enterprise infrastructure right from design, deploy, operate and optimize stages
- New age technological needs of networking automation and network programmability are part of the CCIE certification. CCIE acquires these essential skillsets in the form of CCIE certification
- Incremental recognition is an attractive feature of CCIE certification revamps. You need to clear the qualifying exam and CCIE lab. Passing qualifying exam (SCOR 350-701) entitles you to a specialist certification. It means, after clearing the qualifying exam and lab exam, you get CCIE certificate and specialist certification
- Adding the CCIE certification badge on your social media platforms gives you instant recognition and increases the visibility of your profiles
Prerequisites
To fully benefit from this course, you should have the following knowledge and skills:
- Skills and knowledge equivalent to those learned in New CCNA
- Familiarity with Ethernet and TCP/IP networking
- Familiarity with firewall, VPN, and Intrusion Prevention System (IPS) concepts
- Familiarity with Cisco AnyConnect Secure Mobility Client
- TCP/IP services, including Domain Name System (DNS), Secure Shell (SSH), FTP, Simple Network Management Protocol (SNMP), HTTP, and HTTPS
- Clear understanding of the benefits of site-to-site and Remote Access VPN options
- Basic programming language concepts
These courses are mandatory to help you meet these prerequisites:
Training Outline
- Deploy, implement and troubleshoot Cisco ASA Firewall
- Deploy, implement and troubleshoot Cisco IOS VPN
- Deploy, implement and troubleshoot Cisco L2 Security
- Deploy, implement and troubleshoot Cisco IOS Firewall & Cisco NFP (Network Foundation Protection)
- Deploy implement and troubleshoot Cisco WSA
- Deploy, implement and troubleshoot Cisco ISE (AP & WLC)
- Deploy, implement and troubleshoot Cisco ISE (AP & WLC)
- Deploy, implement and troubleshoot Cisco NGIPS Virtual (VMware)
- Deploy, implement and troubleshoot Cisco ESA
For more in-depth course curriculum information – please check CCIE Security Training Course Curriculum Details
Hands-on Labs
- Switch Port Configuration
- Operation and Implementation of VLAN
- Operation and Implementation of VTP
- Operation and Implementation of STP
- Protecting the Spanning Tree Protocol Topology
- Operation and Implementation of RSTP and MST
- Operation and Implementation of Ether-Channel
- Operation and Implementation of DHCP and DHCP Relay Agent
- Operation and Implementation of NTP
- Operation and Implementation of HSRP, VRRP and GLBP
- Operation and Implementation of Port Mirroring to Monitor Traffic
- Operation and Implementation of Layer 2 Security Technologies
- WSA Topology Introduction and Initial Configuration
- WSA Installation on VMware Workstation and Basics
- Explicit Proxy Mode URL Filtering Using Custom URL Categories
- Explicit Proxy Mode URL Filtering Using Global Policy
- Explicit Proxy Mode Download Limit For HTTP, HTTPS and FTP
- Explicit Proxy Mode IP Base URL Blocking For HTTP, HTTPS and FTP
- Explicit Proxy Mode URL Redirection
- Explicit Proxy Mode Active Directory Integration and Proxy Authentication
- Advanced Web Security: WSA Management and Command Line Interface (CLI) Basics
- Advanced Web Security: WSA High Availability Using VRRP and PAC File
- Advanced Web Security: How to enable HTTPS Proxy on WSA
- Advanced Web Security: Time Range and Volume Quota
- Advanced Web Security: AVC and Web Reputation Configuration Examples
- Transparent Proxy Configuration Labs
- Cisco Identity Services Engine configuration and implementations
- Static and Default Routing on ASA
- RIP, EIGRP, OSPF, BGP,SLA,NAT,CTP on ASA
- Site-Site, Remote Access, SSL VPN on ASA
- VPN Load balancing on ASA
- Transparent Firewall on ASA
- Security Context on ASA
- Failover,MPF,IPv6, OSPFv3,O on ASA
- NAT With IPv6 on ASA
- Site-Site, SSL VPN With IPv6 on ASA
- Advance Firewall Features With IPv6 on ASA
- Dynamic Routing in Multiple Mode on ASA
- Site-Site VPN in Multiple Mode on ASA
- Site-Site VPN IPv6 in Multiple Mode on ASA
- Implementation of IPSec and Cryptography
- Implementation of Site-Site VPN, Remote Access VPN, SSL VPN
- Implementation of DMVPN, GET VPN, Flex VPN and much more
What to expect in the exam
The 8 hours practical exam will assess candidate's skills through the entire network lifecycle of designing, deploying, operating and optimizing complex network scenarios. The exam consists out of 2 modules that are fixed in time and will be delivered in a fixed sequence:
The goal of this module is to measure ability to create, analyze, validate and optimize network designs, which is the base for all deployment activities. Candidates will need to:
- Understand capabilities of different technologies, solutions and services
- Translate customer requirements into solutions
- Assess readiness to support proposed solutions
The module is scenario-based, without access to any devices. Candidates will be provided with a set of documentation required to discern before answering web-based items.
Examples of documentation include email threads, high-level design, network topology diagrams, customer requirements and restrictions, etc. Examples of web-based items include Drag-and-Drop, Multiple-Choice-Single-Answer, Multiple-Choice-Multiple-Answer, Dropdown items, etc.
During this module backward navigation will be disabled. As such, candidates will not have full visibility on all questions within this module. Points value(s) associated to each item are not displayed within this module.
In this module, candidates will be deploying, operating and optimizing network technologies and solutions.
- Deploy: Candidates will build the network according to the design specifications, customer requirements and restrictions. All steps required for a successful network implementation will be covered, including configuring, integrating and troubleshooting the commissioning of technologies and solutions, as per Exam Topics
- Operate and Optimize: Candidates will operate and optimize network technologies and solutions. This includes monitoring network health, network performance, configure the network to improve service quality, reduce disruptions, mitigate outages, reduce operating costs, and maintain high availability, reliability, and security, as well as diagnose potential issues and adjust configurations to align to changing business goals and/or technical requirements
This module provides a setup that is very close to an actual production network environment and will consist of both hands-on (device access) as well as web-based items. Where possible, a virtualized lab environment will be used in this module. Please refer to the equipment and software list for more detailed information.
During this module backward navigation will be enabled. Candidates will have full visibility on all questions within this module. Points value(s) associated to each item are displayed within this module.
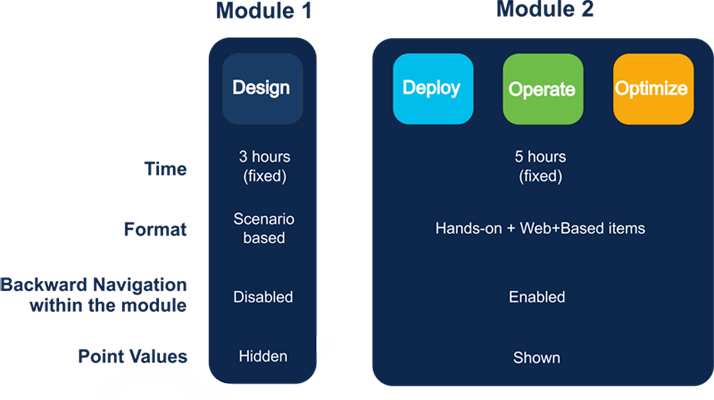
What is the passing score for CCIE Security v6.1 Lab Exam?
Each module has both a minimum score and a pass score. Both minimum and pass scores are set on a per-module basis, based upon exam difficulty level.
- The pass score corresponds with expert level competence
- The minimum score is the absolute minimum score expected from an expert level candidate
To pass the exam, candidates need to score higher than the aggregated pass score of both modules and score higher than the minimum score set on each of the modules individually
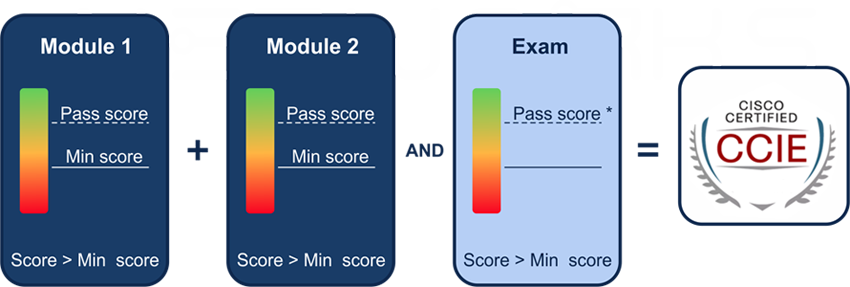
If candidates score less than the overall aggregated pass score of both modules OR score less than the minimum score set on 1 (or more) of the individual modules, they will fail the exam. Upon passing the exam, candidates will not be provided any additional score details.
Candidates that fail the exam will be given a score report, indicating what module(s) they passed or failed. Additionally, candidates will be provided cumulative scoring percentages on a per domain level, across both modules.
What Devices are used during Hands-on Labs?
Our CCIE Security Zero to Hero Training program provides the students with opportunity to have hands-on labs on CCIE Racks which are based on latest CCIE exam blueprints and in return boost their confidence to work with such high end devices efficiently in secured enterprise networks
Virtual Machines:
- Cisco Identity Services Engine (ISE): 2.4
- Cisco Web Security Appliance (WSA): 9.2
- Cisco Email Security Appliance (ESA): 11.1
- Cisco Firepower Management Center Virtual Appliance: 6.2
- Cisco Firepower NGIPSv: 6.2
- Cisco Firepower Threat Defense: 6.2
- Cisco Adaptive Security Virtual Appliance (ASAv): 9.4(3)
- Cisco CSR 1000V Series Cloud Services Router: 15.5.(3), 16.6.3
- Cisco StealthWatch SMC-FC: 6.10
- Cisco FireAMP Cloud: 5.3
- Cisco Wireless Controller (WLC): 8.3
- Cisco DNA Center Release 1.3.1
- L2IOSv: 15.2
Physical Equipment
- Cisco Adaptive Security Appliance: ASA5512: 9.2
- Cisco Adaptive Security Appliance: ASA5516: 9.8
- Router: ISR 1841, 1905, 2811, 2911
- Cisco Catalyst Switch: 3650, 3850
- Cisco Wireless Access Point: AP1852: 8.3
- IP PHONE - 7965
- Tools: Cisco IOS , Putty, GNS and Cisco Packet Tracer
Other
- Test PC: Windows 10 Enterprise
- AD/DNS: Window Server 2016
- Linux Kali: 4.17
- Cisco Anyconnect: 4.2
What Jobs are available after the course?
- Security network engineers
- Consulting systems engineer
- Technical solutions architect
- Network designer
What is included in soft Skills and Personality Development sessions?
Along with Cisco CCIE Technical Training, we also provide Personality Development sessions to groom you like a Professional.
Resume Writing
Presentation Skill
Documentation Skill
Visio Skill
Mock Interivews
with Manager/HR
Group Discussion
Email Etiquette
Soft Skills & Personality Development Classes
Do you provide Placement Assistance, post completion of the training?
We are 100% committed to offer placement assistance to our students. Industry approved Resume Templates are provided to candidates as guidance to assist them in writing their resumes. We also provide students with FAQ interview questionnaire to help them prepare for their job interviews.
What is the training and placement process?
What is expected salary after the CCIECollaboration Zero to Hero training program?
Exam
| Exam Name | Exam Code | Duration | Cost | Registration: |
|
Implementing and Administering Cisco Solutions |
200-301 CCNA |
2 Hours | 300USD | Pearson VUE |
|
Implementing Cisco Enterprise Advanced Routing and Services |
300-410 ENARSI |
2 Hours | 300USD | Pearson VUE |
|
Securing Networks with Cisco Firepower Next-Generation Firewall (SSNGFW) |
300-710 SNCF |
2 Hours | 300 USD | Pearson VUE |
|
Implementing and Operating Cisco Security Core Technologies |
350-701 SCOR |
2 Hours | 400USD | Pearson VUE |
|
CCIE Security v6.1 |
- |
8 Hours | 1600USD | CCIE Portal |
Lab Setup
Demo
Training Plan & Schedule
Training Plan
| CCIE Security v6.1 Zero to Hero Training | |||
| Batch | Weekdays (Mon-Fri) | Weekend (Sat-Sun) | |
| Mode | Classroom / Online | Classroom / Online | |
 |
Hours | 3 Hours / Day | 4 Hours / Day |
| Duration | 8 Months | 12 Months | |
| Date | Course | Training Type | Batch | Register |
| 6 July 2020 | CCIE Security v6.1 Zero To Hero | Classroom / Online | Weekdays (Mon-Fri) | Enquire now |
| 11 July 2020 | CCIE Security v6.1 Zero To Hero | Classroom / Online | Weekend (Sat-Sun) | Enquire now |
| 20 July 2020 | CCIE Security v6.1 Zero To Hero | Classroom / Online | Weekdays (Mon-Fri) | Enquire now |
| 25 July 2020 | CCIE Security v6.1 Zero To Hero | Classroom / Online | Weekend (Sat-Sun) | Enquire now |
What students say about us

Jerry Mpho Kekana
Octa Networks Thank you for a great opportunity you provided me in my CCIE Security bootcamp, looking forward to completing my lab journey with the institution, Much appreciated.

Rahul Deo Burman
I am taking ccna security class by Munnawar khan.His teaching style us wonderful and having in depth knowledge. Thanks to Octa Network for providing this great opportunity to learn the IT skills

Seema Lachhani
Great place to learn technology. I have seen careers made in @octanetworks. Octa networks will make you an Expert within a span of 6 months
Frequently Asked Question
Course duration depends upon whether you opt for regular or weekend batch. If you opt for regular batch then the duration will be 6 months and if you opt for the weekend then the course duration will be 12 months.
We provide renowned, expert, and industry certified trainers having industrial experience of at least 3 years. Our technical team members are well-groomed, experienced, and expert in their respective area of specialization.
We provide 100% placement guarantee. In fact, Octa Networks is the only cisco training Institute in India to give you “On Paper Job Guarantee” the day you enroll for our CCIE Security Zero to Hero program. However, for other courses we provide 100% Placement assistance for interview and job alert.
No. It’s absolutely FREE for students enrolling our CCIE Zero to Hero program. However its chargeable for students who have enrolled trainings other than CCIE Zero to Hero program.
Yes. There will be enough number of doubt clearing sessions. Some of our experienced mentors will be guiding you on the respective topics.
Students are provided with rigorous hands-on lab sessions, industry experts’ sessions, practice tests, group discussions, technical presentations, resume preparation, interview preparation, and much more
After the clearance of the course fee payment students will be informed via call, E-mail or sms.
Yes, the student can enroll for more than one course. We appreciate student’s eagerness and readiness for more courses and provide proper guidance
Get Service Price In India
We Provide Services In
Stay Informed
Keep current with our new updated training & certifications, offers and more.










.png)
.png)





